Apple’s official iOS App Store is well known for its strict code review of any app submitted by a developer. This mandatory policy has become one of the most important mechanisms in the iOS security ecosystem to ensure the privacy and security of iOS users. But we recently identified an app that demonstrated new ways of successfully evading Apple’s code review. This post discusses our findings and potential security risks to iOS device users.
Apple’s official iOS App Store is well known for its strict code review of any app submitted by a developer. This mandatory policy has become one of the most important mechanisms in the iOS security ecosystem to ensure the privacy and security of iOS users. But we recently identified an app that demonstrated new ways of successfully evading Apple’s code review. This post discusses our findings and potential security risks to iOS device users.
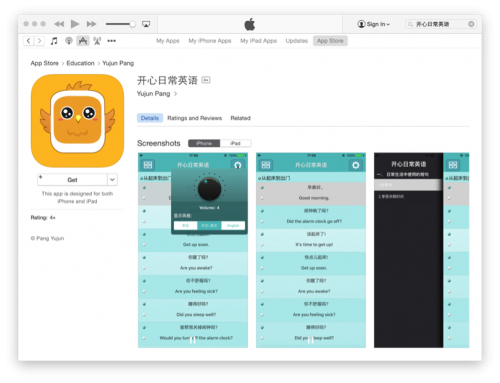
The app we identified is named “开心日常英语 (Happy Daily English),” and it has since been removed by Apple from the App Store. This app was a complex, fully functional third party App Store client for iOS users in mainland China. We also discovered enterprise signed versions of this application elsewhere in the wild. We had not identified any malicious functionality in this app, and as such we classified it as Riskware and have named it ZergHelper.
ZergHelper presents several security risks, include the following:
- It provides installation of modified versions of iOS apps whose security can’t be ensured..
- It abuses enterprises certificate and personal certificates to sign and distribute apps, which may include code that hasn’t been reviewed, or abuse private APIs.
- It asks user to input an Apple ID while it also shares some Apple IDs to users. It will log in to an Apple server using these IDs to perform many operations in background.
- Its author is trying to extend its capabilities via dynamic updating of its code, which could further bypass iOS security restrictions.
- It uses some novel techniques that are sensitive and risky – techniques that could be used by other malware to attack the iOS ecosystem.
ZergHelper appears to have gotten by Apple’s app review process by performing different behaviors for users from different physical locations on earth. For users outside of China, it would act as what it claimed: an English studying app. However, when accessing the app from China, its real features would appear… Click HERE to read more